Even as government and security agencies are working to fight cybercrime and data breaches, the incidents of identity thefts are on the rise. If you have always been under the impression that only businesses are at risk, know that as an individual, you could take several steps to safeguard your Personally Identifiable Information (PII) from hackers. Every piece of information that relates to you can be used to steal your identity, clean out your bank account, make purchases in your name, and even commit crimes.
Eva Velasquez is the president and CEO of the Identity Theft Resource Center. She talks about the importance of safeguarding details like your email address, Social Security Number, telephone number, credit card number and CVV, medical records, passwords, and any other data that can be traced back to you. Eva reveals to US News, “The ramifications of identity theft are terrifying.” You stand to lose more than your identity and finances; you also risk your life.
Here are a few steps you can take to protect you from the ever-advancing strategies that cybercriminals and hackers use.
1. Dispose of Your Electronics Securely:
You probably use a bunch of electronics around the house like a computer, laptop, tablet, and of course, cell phones. With the barrage of apps available for just about all the functions you can think of, most people use their gadgets to file taxes, apply for credit cards and pay off bills, and conduct online shopping, to name a few. Each time you use a device, it stores your PII along with a ton of other data in its hard drive – and sets you up for identity theft. Should you discard the gadget without removing this data, you’re leaving it open for hackers to get their hands on it. Be aware that cybercriminals only need to buy the old electronics and scan them for the information they can use.
A smart move is to destroy confidential or sensitive information with All Green recycling solutions, one of the certified agencies that take care of your old gadgets, securely and responsibly. They’ll remove the hard drives and wipe them or shred them using government-approved protocols so that even the most sophisticated hackers cannot decipher the data.
2. Surf the Internet with Caution:
You may have read about phishing websites that have been set up for the sole purpose of harvesting the details that surfers enter when landing on the sites. A good way to identify potentially dangerous sites is to look for the padlock icon next to the web address and to ensure that the site carries the “https://” sign. However, like the statistics released by KrebonSecurity tell you, 49% of phishing websites now carry the padlock logo. The agency also warns that such sites mimic authentic sites so closely that it is virtually impossible to detect the difference. If you’re one of the 80% of internet users who believe that the logo offers security, think again. To protect you from identity theft, you might want to rely on reputed browsers like Google that issues alerts telling you that a particular website is fraudulent.
3. Get a Secondary Email Address for Surfing and Shopping:
Using a single email address is no doubt convenient when you can receive all your communication in one location that you can open and check. Each time you surf the internet and the site asks for your email address, you’re raising the risk of the ID getting harvested and sold. A better option is to generate a secondary email ID that is different from the one you use most commonly for all important tasks. Use it for shopping, browsing, filling forms, or in any other location that is even remotely unreliable and prevent the possibility of identity theft.
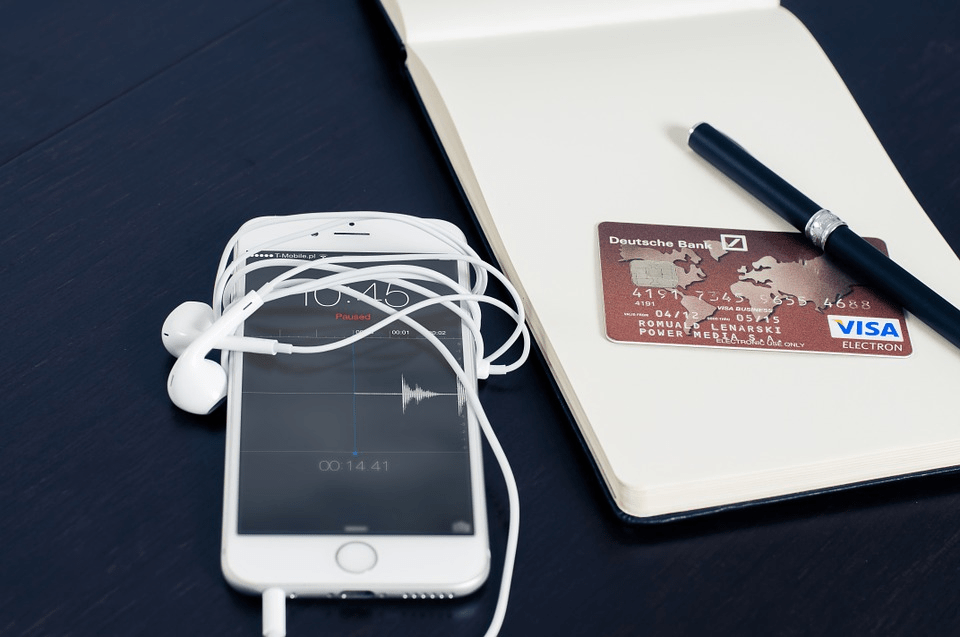
4. Use a Separate Credit Card for Online Purchases:
Given that harvesting credit card numbers and CVVs is the most common of cybercrime, buy separate credit cards for shopping. Like this article on CNET advises, you can choose from the many Internet-only cards available that are not linked to your bank. In this way, even if you lose the details of the card and it gets hacked, your bank account remains secure and cannot get wiped clean. Most credit cards offer the facility of sending you alerts each time you make a transaction on them. Sign up for this option because hackers are likely to steal small amounts to test if you detect the intrusion before making large purchases.
5. Be Cautious When You Use Social Media Sites:
Setting up accounts on social media sites raises your vulnerability to identity theft in more ways than you can imagine. Most users tend to add their birth dates, addresses, phone numbers, and other information. All of this data can be easily accessed by hackers who can use it to decipher passwords and track your activities to identify spending habits. In case you’ve signed up for the multi-step authentication protocol, remember that you need not to add accurate information to the security questions. For instance, even you didn’t own a pet, it’s okay to put down your first pet’s name as “Rover.” For a more in-depth understanding of how phishing on social media works, check out this feature on Experian.
6. Use Secure Passwords:
Passwords are your first line of defense against hackers and identity theft. The more complicated you can make them, the more secure you are. Also, add the multi-step authentication and you have a safe strategy. If you aren’t quite confident about generating hard-to-detect passwords, use apps that can create passwords for you. Only remember to save them in a secure location which is entirely off the internet. Using the old-fashioned pen and notebook is a great option. And, remember to change all passwords regularly.
Identity theft is a threat that grows larger with each passing year. Even as the authorities work to strengthen their measures for cybersecurity, hackers and cyber criminals are devising more sophisticated tools and strategies to get around, those measures. As an aware individual, you can take the necessary steps to safeguard your PII and prevent it from getting leaked on the internet.
Read Also: